Bootkit: How to Detect and Prevent This Stealthy Threat
A bootkit is one of the most dangerous types of malware, capable of embedding itself deep into your system’s boot process. Unlike regular malware, a bootkit infects the Master Boot Record (MBR) or Unified Extensible Firmware Interface (UEFI), allowing it to remain hidden even after system reboots and OS reinstalls.
We’ll break down how bootkit malware work, how to detect them, and the best ways to prevent an infection on your Windows PC.
What Is a Bootkit?

A bootkit is a form of modern rootkit malware that manipulates the boot process, allowing attackers to gain persistent control over a system. Since bootkits infect critical areas like the MBR or UEFI firmware, they can bypass traditional security measures, making them extremely difficult to detect and remove.
How Does a Bootkit Work?
- Initial Infection – A bootkit can enter your system through malicious downloads, phishing emails, or infected USB drives.
- Boot Process Manipulation – Once installed, the bootkit modifies the MBR or UEFI firmware, ensuring it loads before the OS.
- System Takeover – The bootkit grants attackers complete control over your device, allowing them to steal data, install more malware, or even disable security software.
How to Detect a Bootkit on Windows?
Since bootkits operate at a low level, they often evade traditional antivirus detection. However, you can still uncover them using these methods:
1. Check for System Anomalies
- Unexpected system crashes or random reboots
- Boot failures or blue screen errors
- Inability to access BIOS/UEFI settings
2. Scan for Rootkits and Bootkits
Use specialized security tools that can inspect the boot sector and firmware:
- Windows Defender Offline Scan
- Fortect’s Real-Time Malware Protection
3. Verify Boot Configuration
You can manually inspect your system boot records with the Windows Command Prompt:
- Open Command Prompt (Admin)
- Run the following command to check your boot record:
- powershell
- CopyEdit
- bootrec /scanos
3. If unknown OS entries appear, your boot sector may be compromised.
How to Prevent Bootkit Infections?
To prevent bootkit attacks, follow these best practices:
1. Enable Secure Boot in BIOS/UEFI
Secure Boot ensures only trusted software runs during startup. To enable it:
- Restart your PC and enter BIOS/UEFI (usually by pressing F2, F10, or DEL).
- Go to the Boot section and enable Secure Boot.
- Save changes and exit.
2. Keep Windows and Firmware Updated
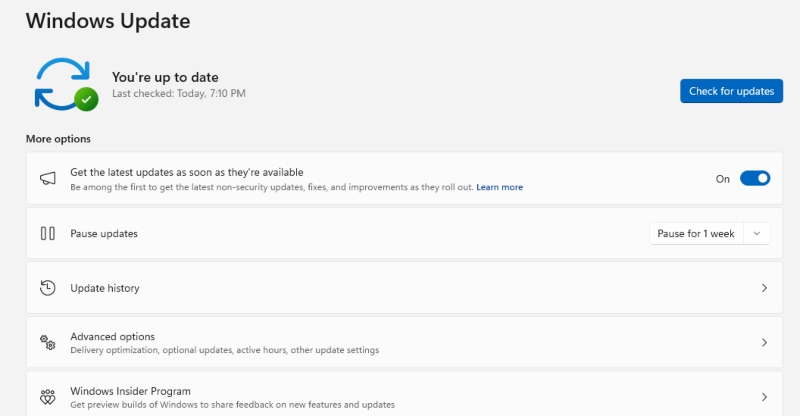
Regular updates patch security vulnerabilities that bootkits exploit. To update:
- Press Win + I to open Settings.
- Go to Update & Security > Windows Update.
- Click Check for updates and install any available updates.
3. Restrict User Permissions
Limiting admin access prevents unauthorized system modifications. To do this:
Method 1:
- Press Win + X and select Computer Management.
- Navigate to Local Users and Groups > Users.
- Right-click on an account and choose Properties.
- Under Group Membership, change from Administrator to Standard User.
Method 2:
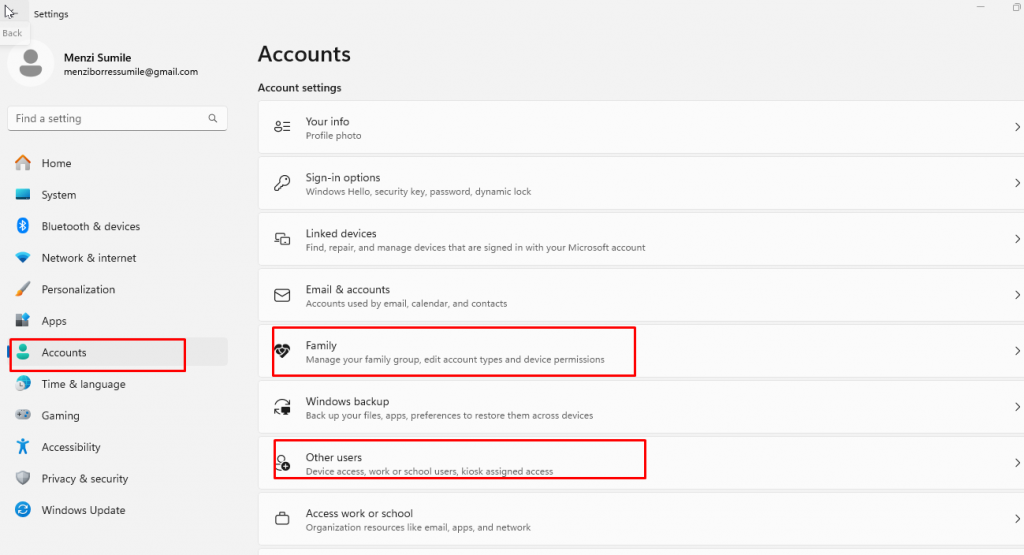
1. Press Win + I to open Settings.
2. Go to Accounts > Family & other users.
3. Select the user account and click Change account type.
4. Choose Standard User instead of Administrator.
Click OK to apply changes.
4. Use a Security Tool with Real-Time Malware Protection
Sure, Windows Defender can defend and protect your computer from known threats or malware from outside sources. However, bootkit malware is so modern and sophisticated that uses rootkit tools to invade detection. This is why we need a modern and more enhanced security tool such as Fortect.
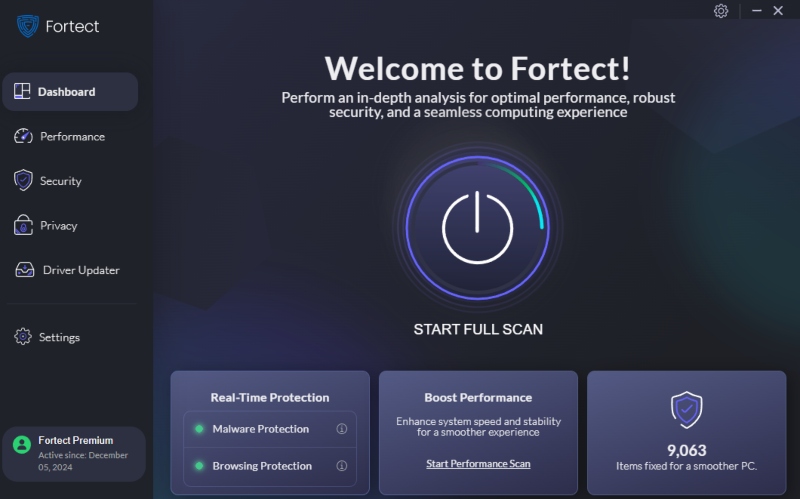
Fortect is an all-in-one security tool with real-time malware protection and automatic scanning. It continuously scans for any threats and blocks them before they can infect your system such as bootkits malware. It provides deep system analysis, ensuring hidden malware doesn’t go undetected.
Download Fortect now.
How to Remove a Bootkit from Windows 10/11?
If your system is infected with a bootkit, follow these steps:
Boot into Safe Mode
- Press Win + R, type msconfig, and hit Enter.
- Go to the Boot tab, check Safe boot, and click OK.
- Restart your PC to enter Safe Mode.
Use Windows Defender Offline Scan
- Open Settings > Update & Security > Windows Security.
- Click Virus & Threat Protection> Scan options.
- Select Windows Defender Offline scan and click Scan now.
- Let Windows restart and remove detected threats.
Repair the Boot Sector
- Open Command Prompt (Admin) then choose Yes from the second window.
- Type the following commands, pressing Enter after each:
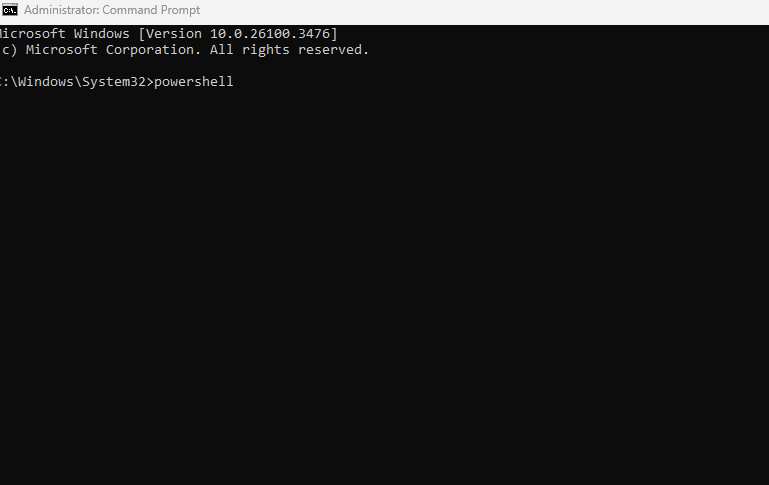
- powershell
- bootrec /fixmbr
- bootrec /fixboot
- bootrec /rebuildbcd
3. Restart your computer and check if the issue persists
Final Thoughts
Bootkits are among the most dangerous threats, allowing attackers to take full control of your system. Since they embed themselves deep into the boot process, detecting and removing them requires specialized tools and manual intervention. By enabling Secure Boot, keeping Windows updated, and using real-time protection tools like Fortect, you can safeguard your system from bootkit infections.




