Deepfake Phishing Attacks on Windows: How to Stay Safe
Deepfake phishing attacks use artificial intelligence to create highly convincing fake audio, video, or text messages. Cybercriminals manipulate media to impersonate trusted individuals, such as coworkers, managers, or even customer service representatives, tricking victims into revealing sensitive information or executing financial transactions.
These attacks are especially dangerous because they exploit human trust, making traditional security awareness training insufficient. Windows users must be vigilant and adopt proactive security measures to detect and prevent these threats.
How Do Deepfake Phishing Attacks Work?
Deepfake phishing attacks typically follow these steps:
- Data Collection: Hackers gather publicly available audio, video, or text samples from social media, emails, or leaked databases.
- AI Manipulation: Using deep learning algorithms, attackers generate realistic fake content mimicking a trusted individual.
- Phishing Attempt: The attacker sends an email, makes a phone call, or conducts a video meeting to manipulate the target into performing actions such as transferring funds or disclosing login credentials.
- Execution of Fraud: Once the target complies, attackers gain unauthorized access to sensitive systems, steal funds, or execute cyber espionage.
How to Identify Deepfake Phishing Attacks
Detecting deepfake phishing attacks requires a combination of skepticism and technological tools. Here are some signs to watch for:
1. Unusual Requests

Be wary of unexpected or urgent requests, especially those asking you to transfer money, share sensitive credentials, or provide personal information. Cybercriminals often create a sense of urgency to pressure victims into acting without verifying the request. If the request seems out of the ordinary or comes from an unfamiliar source, take a moment to confirm its legitimacy through official channels before responding.
2. Voice and Video Inconsistencies
Deepfake videos may exhibit unnatural eye movements, blurred lip-syncing, or awkward pauses. Similarly, deepfake audio may lack natural intonation or have robotic glitches.
3. Unverified Communication Channels
If you receive a call, video request, or message from an unfamiliar number or unexpected source, proceed with caution. Cybercriminals often use deepfake technology to impersonate trusted individuals or organizations. Before engaging, verify the request through official channels, such as directly contacting the person or organization via a known phone number or email.
Never rely solely on the incoming communication, as it could be a sophisticated phishing attempt.
4. Poor Video or Audio Quality

While deepfake technology has advanced, some forgeries still exhibit noticeable flaws. Look for pixelation, unnatural facial movements, mismatched lip-syncing, or audio delays. These inconsistencies can indicate an AI-generated manipulation rather than a genuine video or voice call.
If something feels off, verify the sender’s identity through another trusted method before taking any action.
How to Protect Yourself from Deepfake Phishing Attacks
1. Enable Multi-Factor Authentication (MFA)
MFA ensures that even if an attacker acquires login credentials, they cannot access accounts without a second verification step.
2. Verify Requests Through a Secondary Method
Always confirm sensitive requests through an alternative channel, such as an official email or direct phone call.
3. Educate Yourself and Your Team

Security awareness training is essential to help individuals recognize and respond to deepfake threats. Training should include real-world examples of deepfake phishing attempts, signs to watch for—such as unnatural facial movements or audio inconsistencies—and steps to verify suspicious requests. Encourage a culture of skepticism where employees or team members question unexpected or urgent requests, especially those involving financial transactions or sensitive information.
Staying informed about emerging deepfake tactics can significantly reduce the risk of falling victim to these advanced scams.
4. Keep Your Windows System Secure
Updating your Windows system regularly ensures that vulnerabilities exploited by cybercriminals are patched. Use trusted security software to add an extra layer of defense.
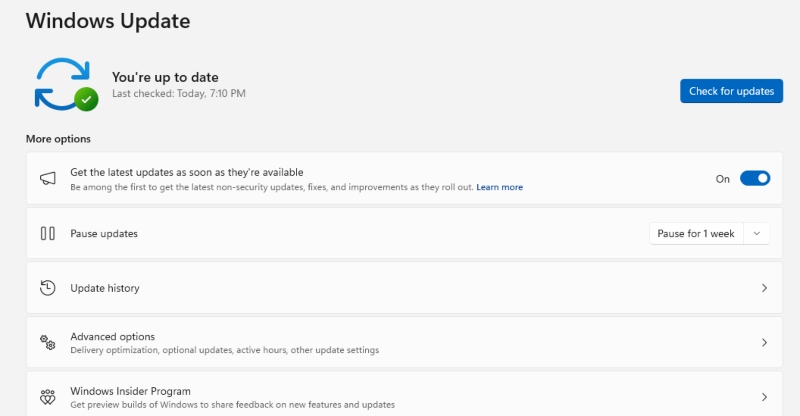
How to Check if Windows 10 is Up to Date:
- Open Settings – Press Win + I to open the Settings menu.
- Go to Update & Security – Click Update & Security > Windows Update.
- Check for Updates – Click Check for updates and install any available updates.
- Restart if Needed – Restart your PC to apply updates.
Fortect: Your All-in-One Security Solution

Deepfake phishing attacks can exploit system vulnerabilities, making it crucial to have reliable security software. Fortect offers an all-in-one PC repair solution with real-time malware protection. It automatically scans your Windows PC for threats, ensuring your system stays secure against deepfake phishing attacks and other advanced cyber threats. Protect your Windows system today with Fortect.
Download and install Fortect today.
Final Thoughts
Deepfake phishing attacks are evolving, making it imperative for Windows users to stay informed and proactive. By recognizing the warning signs, verifying unusual requests, and leveraging security tools like Fortect, you can significantly reduce the risk of falling victim to these sophisticated scams. Stay alert, stay secure.




